SAML Configuration
LogMeOnce provides a unified federation solution which allows configuring and managing multiple IdPs and provide access using Adaptive Authentication solution based on users, roles and access. By defining one or more IdPs, you will be able to configure LogMeOnce as a service provider (SP) and use external identity providers (IdP) to Single Sign-On (SSO) into LogMeOnce.
- Login to your LogMeOnce administrator account with privileges to create SAML identity Provider
- Select Go to Administrator Console
- Select Security Then Select Identity Provider
- Click +Add Identity Provider and select a predefined configuration or a default SAML configuration.
The following shows an example of Identity Provider configuration.
Name: Enter a name for your IDP (Ex. Okta, Salesforce, Azure).
Issuer: Copy the Issuer value from your IdP provider (Ex. Okta, Salesforce, Azure, etc.). This is a required field. You may enter any text, and continue to update this filled later.
Identity Provider Certificate: Download it from your IdP provider and upload it.
Identity Provider Login URL: Copy and paste it from your IdP provider.
Identity Provider Logout URL: It can be the same as your Okta Sign in URL, or any URL that you want your users to get redirected to.
External Identity Providers (SAML)
The Identity Provider allows you to configure LogMeOnce as a Service Provider (SP) and use your external Identity Providers (IdP) to Single Sign-On (SSO) into LogMeOnce.
External IdP can authenticate your existing users and by enabling Just-In-Time (JIT) provisioning, thus users will be created in LogMeOnce if their account doesn’t exist. Users are always matched with their username against SAML assertion subject identifier (saml:NameID). Your IdP may also provide additional attributes along with SAML assertion that will be mapped to your user profile. List of supported attributes are:
- firstName
- lastName
- birthdate
- gender
- address
- city
- state
- zip
- country
- company
- jobTitle
- website
Custom attributes are supported and will be saved along with their key-value pairs.
Single Sign On (SSO) and Adaptive Authentication
Once both LogMeOnce (Service Provider or SP) and Identity Provider (IdP) are properly configured, then users can login. The following SSO options are supported:
- SP side initialized
- IdP side initialized
If your LogMeOnce account is licensed for “Adaptive MFA authentication” add-on, you have the following consideration for users:
- If you have not configured MFA (Ex. addition factors), users will follow the SSO flow, which will then IdP handles user authentication.
- If you have configured MFA - by default users will follow the SSO flow, and IdP handles user authentication. Your IdP will be shown as part of an authentication option which you can select it to be displayed (promoted) and shown in LogMeOnce login page.
Just-In-Time (JIT) Provisioning
By enabling Just-In-Time provisioning LogMeOnce will create new users if it is not matched against existing LogMeOnce user. New user will be activated if your user limit is not exceeded. In case of reaching your user limit, LogMeOnce will allow you create users, but such users will not be activated. Those "over the limit" users can’t login into LogMeOnce, but their access requests and action(s) are logged and saved into your Activity Log.
Key Management Service
LogMeOnce employs a zero-knowledge policy. Your critical data are encrypted using cryptography keys , which are encrypted too. All encryption tasks are performed on the client side and it is NEVER accessed by LogMeOnce servers. This means cryptography keys are accessed at the client side only. We always protect those keys by "something" that users know (like password, or mobile device, or security answer).
Its an industry know fact that combing Single Sign-On and zero-knowledge technology together, is a challenging solution to solve. That is because the user is supposed to login automatically, and without entering any information. In order to adhere to zero-knowledge technology to protect you and support SSO, LogMeOnce employs Hardware Security Modules (HSM). Your encryption key will be protected by Amazon's Key Management Service (KMS) using “Customer managed key”. LogMeOnce server-side does not communicate with AWS KMS service at any time and all communication will be done by the client side (user). This will provide a protected SSO solution by employing zero-knowledge technology.
We provide extensive key management solutions to choose from, which are listed below;
- Use LogMeOnce KMS Service
- Create your own KSM service at Amazon AWS
- Use your organizations on-premise encryption certificates or HSM
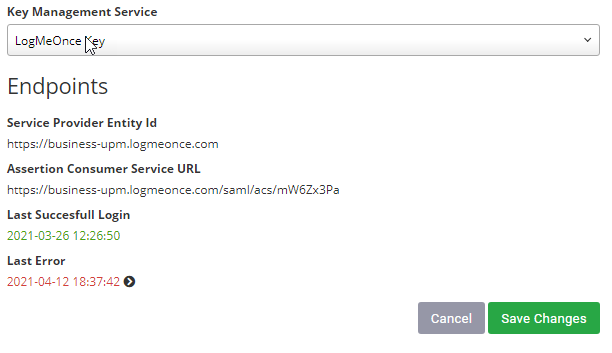
This Key Management can be configured under Administrator Console -> Settings -> Key Management
By adding your own KMS Key all newly created Identity Providers (IdPs) will use your KMS service by default. You may modify the existing Identity Providers that uses LogMeOnce KMS Service to use your own KMS key.
SAML Errors and Logs
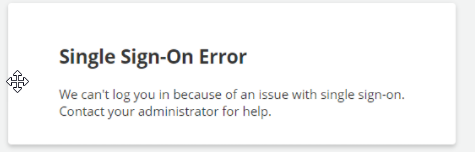
In case of error or SAML misconfiguration, users will see the following error message:
As an Administrator, you have access to error details. You can edit the Identity Provider and see the status of IdP, and whether it was successful or failed SSO attempts.
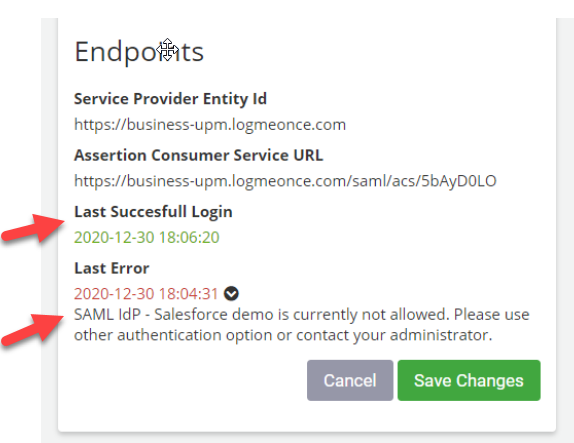
You can also review the events in Activity Log.
Your SAML configuration is completed.
Comments
Article is closed for comments.